Solving Dakotacon 2015 RE C2 challenge with Angr
Background
The motivation my last entry was to provide an easier way for me, and others, to learn more about (and use!) Angr.
Well, I’ve finally had some time to play around with Angr, and I’ve been able to use it to solve two CTF challenges (as of now – I’m still working on some others!): One is the C2 challenge from the Dakotacon 2015 RE challenge, and the other is the first challenge of the 2016 FLARE-ON CTF. This post will cover the former – I plan on releasing the code/writeup for the latter after the 2016 FLARE-ON CTF is over.
I originally solved the C2 challenge using “traditional” reverse-engineering, poking around with IDA pro and looking at the assembly. Since I knew what the correct answer was and approximately how long it too me to get there, I thought it would be interesting to see how long it took me to solve the challenge with Angr. Hint: much longer. :) But, as I become more familiar with Angr, and as a few aspects of Angr improve, I can totally see Angr becoming the quicker route to success in the future.
The goods
Anyway, take a look at the Angr solution (which I’ve commented as best as I can for the time being) HERE.
And if you want the .ipynb file, you can grab that HERE!
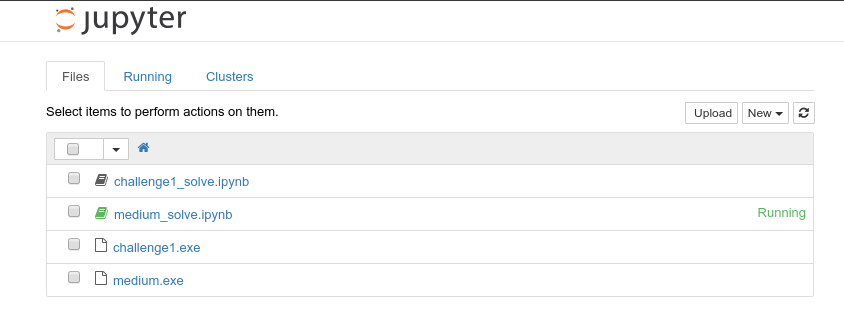
If you’re wondering how to use Angr in Jupyter… well, it’s really easy! It’s just like using Jupyter, and as far as uploading binaries goes (so Angr can actually open/analyze them), just use the Upload button, visible in this screenshot:
Once you’ve uploaded your ELF/.exe/whatever, just open it as an Angr Project in your Angr script, like I did in my example above, and away you go!